加入 Mergeek 福利群
扫码添加小助手,精彩福利不错过!
若不方便扫码,请在 Mergeek 公众号,回复 群 即可加入
- 精品限免
- 早鸟优惠
- 众测送码
The Breaker: Hacker Simulator
教育安全工具,模拟密码破解并本地分析结果
 分享
分享


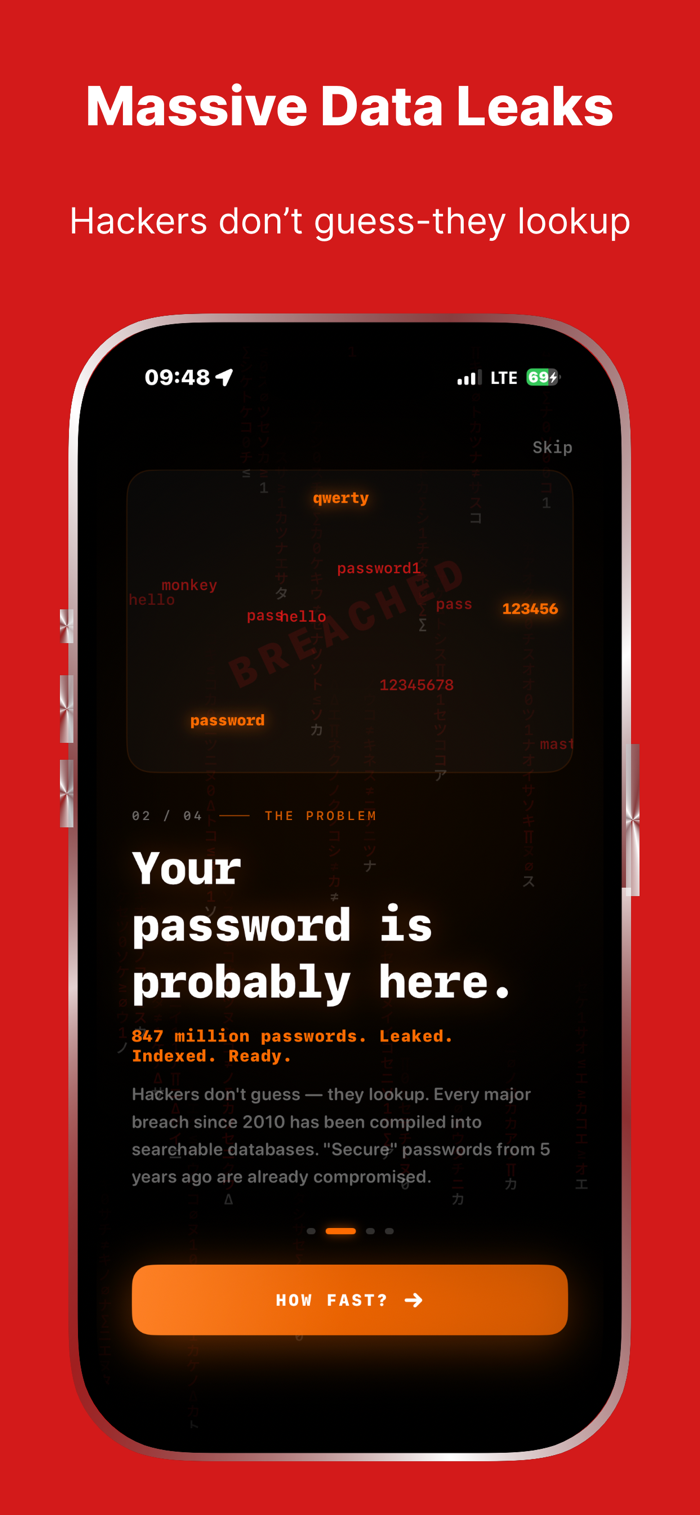
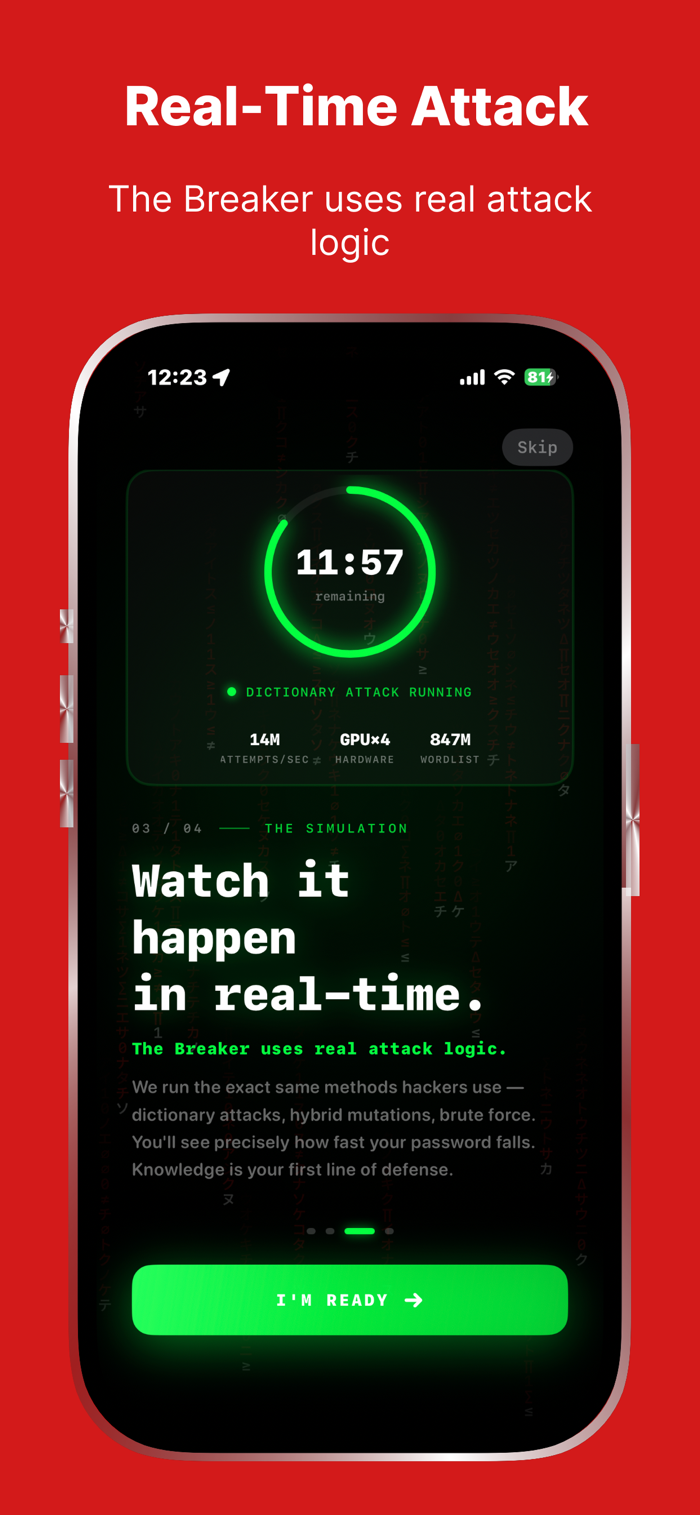
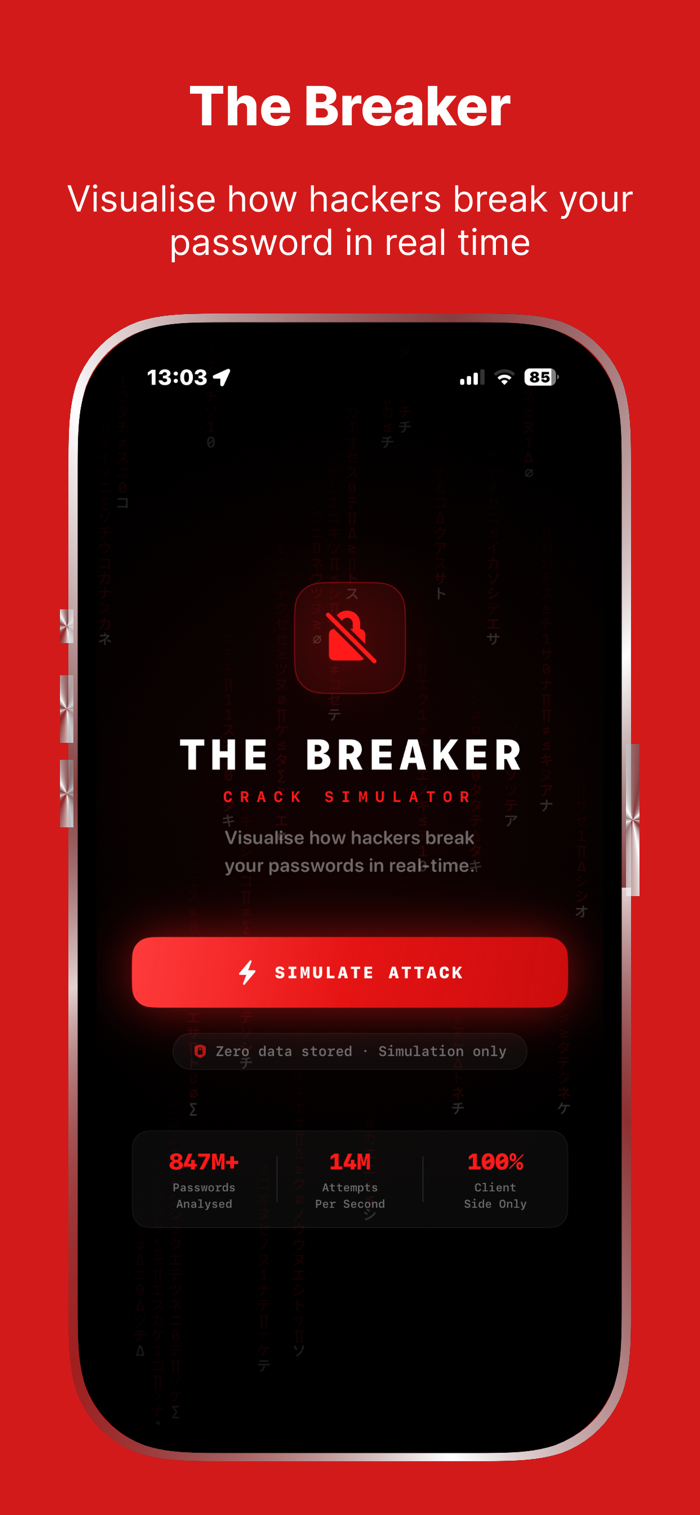

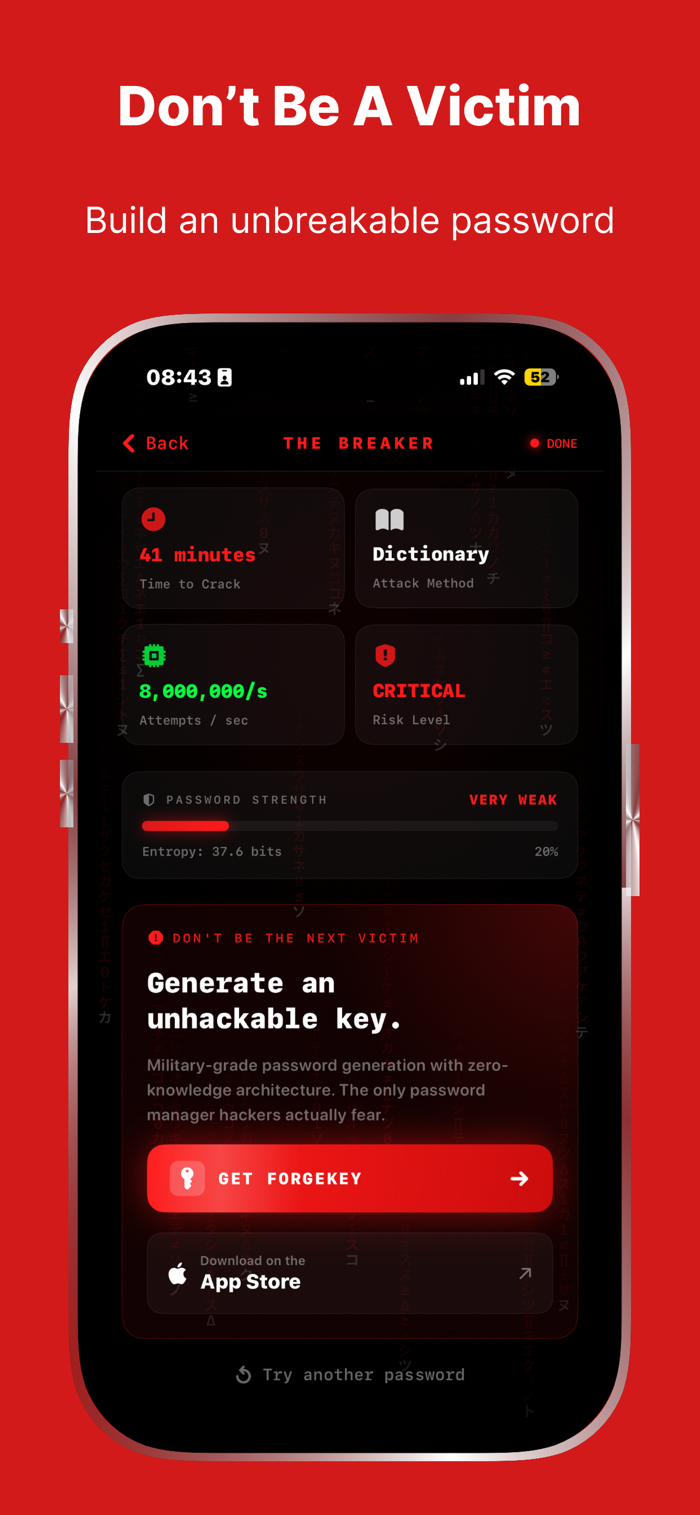


The Breaker是一款教育安全工具,能模拟攻击者用现实方法破解密码。它针对常见攻击向量分析密码,包括字典攻击、混合变异、暴力破解模式分析及实时逐字符可视化。使用时输入密码测试,app进行攻击模拟,在终端式界面查看分析结果,如预估破解时间、攻击方法和风险等级,还能了解密码强弱原因。分析在本地设备进行,密码不传输存储。
用户评价
立即分享产品体验
你的真实体验,为其他用户提供宝贵参考
💎 分享获得宝石
【分享体验 · 获得宝石 · 增加抽奖机会】
将你的产品体验分享给更多人,获得更多宝石奖励!
💎 宝石奖励
每当有用户点击你分享的体验链接并点赞"对我有用",你将获得:
🔗 如何分享
复制下方专属链接,分享到社交媒体、群聊或好友:
💡 小贴士
分享时可以添加你的个人推荐语,让更多人了解这款产品的优点!
示例分享文案:
"推荐一款我最近体验过的应用,界面设计很精美,功能也很实用。有兴趣的朋友可以看看我的详细体验评价~"
领取结果